User management via SAML2
LUY can be set up to authenticate users via SAML2 and an identity provider (IDP).
Please contact LUY support to set up the SAML2 authentication.
LUY matches its own roles with the user groups sent by the identity provider (IDP).
For example:
User Alice is part of the groups "admin" and "employee". In LUY the roles "admin" and "architect" are already present. When Alice logs into LUY, the group "admin" is matched to the LUY role "admin" because they share the same name. The group "employee" as well as the LUY role "architect" are ignored since there is no match for them. Alice is then assigned the permissions of the LUY role "admin".
Prerequisites
In order to use LUY with the identity provider (IDP) the following must be available:
An identity provider (IDP) which allows authentication via SAML2
The link to the metadata of the identity provider (IDP)
The metadata from the identity provider (IDP)
The identity provider (IDP) must send the following attributes to LUY
Last name
First name
Login
Email
Usergroups or IDs for matching the "role" in LUY
The possibility to create a "keystore" on a system console (CMD/Linux terminal)
iTURM and REST requests
The REST interface requires basic authentication in LUY. For this, an iTurm instance is necessary.
SAML2 cannot be used for basic authentication. Log into iTURM and create a technical user to use for basic authentication. You need a LUY role for the permissions of this user. Create or use an existing LUY role and create a role with the same name in iTURM. Then add users to this role.
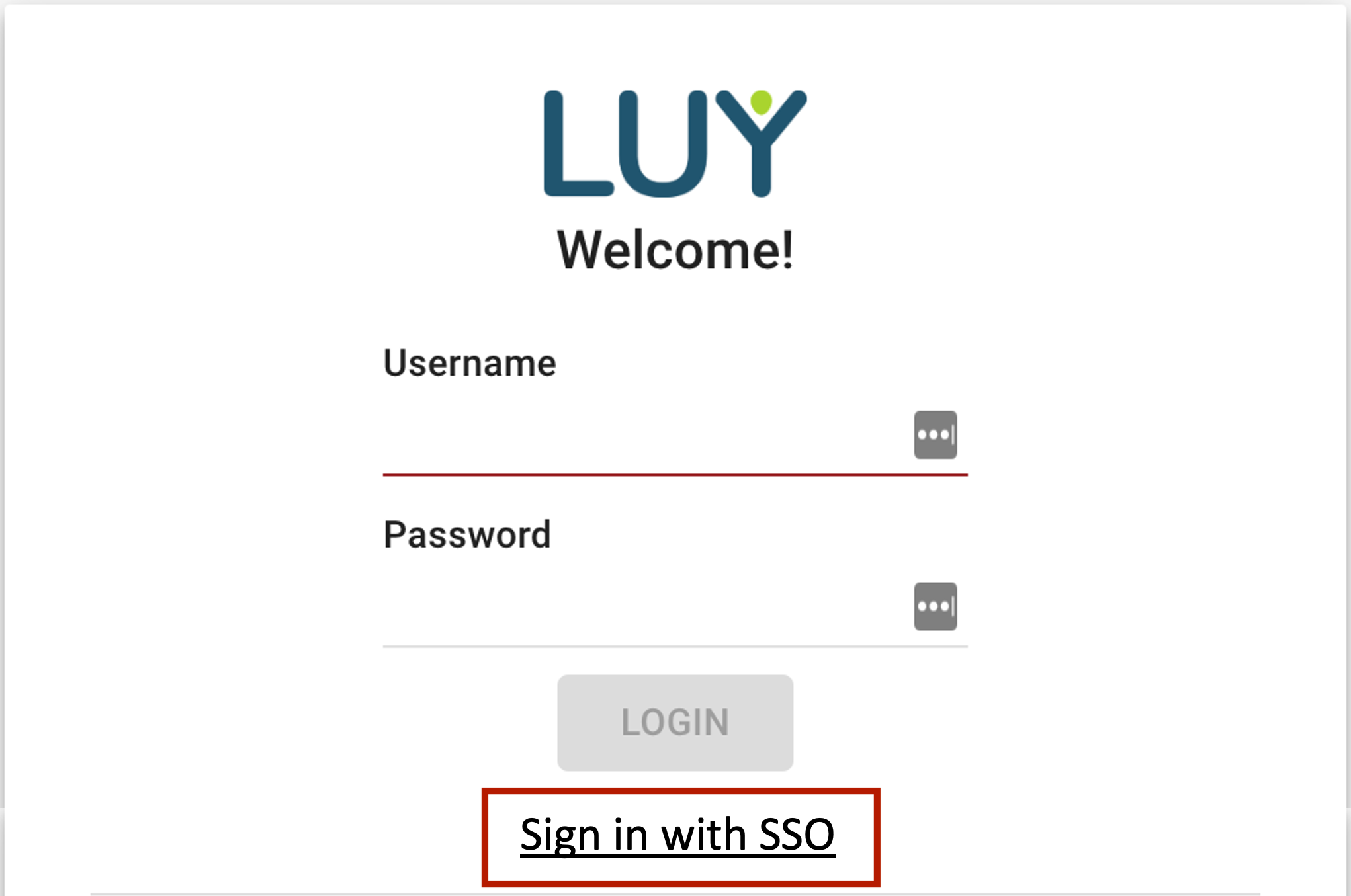
Sign in with SAML2
Upon successful setup of SAML2 for LUY, the login screen will present the option to “Sign in with SSO”. Click here to access LUY.
Username and password entry are disabled in this setting.